UC account provisioning shouldn’t slow onboarding, create security vulnerabilities, or consume valuable IT resources. Yet many organizations still rely on manual user provisioning process flows that turn straightforward access requests into multi-day ordeals filled with errors and inconsistencies. Each manual step in the user access provisioning process introduces risk and delays the productivity that modern UC platforms are designed to deliver.
Automated UC provisioning transforms account management from a reactive scramble into a proactive, systematic process. Instead of wrestling with complex configurations, UC provisioning automation tools enable IT teams to deploy comprehensive UC environments in minutes while maintaining strict compliance standards.
In this step-by-step guide, we’ll show you exactly how automation tools streamline each phase of the user provisioning and deprovisioning process, with specific tool callouts so you can see what this workflow looks like in your environment.
Why Your Current Manual User Provisioning Process Flow Creates More Problems Than It Solves
Traditional account provisioning processes worked when UC environments were simple and employee onboarding happened at a predictable pace. Today’s organizations face entirely different challenges that expose critical limitations of manual user access provisioning processes.
Human Error Multiplies Across Complex Systems
Modern UC environments typically span multiple platforms—voice systems, video conferencing, messaging applications, and collaboration tools. Each platform requires specific configurations, security settings, and integration parameters. When IT administrators handle these tasks manually, even small mistakes cascade across systems, creating security gaps or access failures that can take days to diagnose and resolve.
READ MORE: Two Biggest Errors Caused by Manual UC User Provisioning (& Why They Happen)
Inconsistent Security Implementation
Manual processes rely on human memory and documentation that quickly becomes outdated. One administrator might implement multi-factor authentication correctly, while another overlooks critical security settings. These inconsistencies create vulnerabilities that can compromise entire UC management environments.
Resource-Intensive Operations
With manual provisioning, IT teams spend hours configuring individual accounts instead of focusing on strategic initiatives. This time investment doesn’t scale effectively—adding more users means proportionally more administrative overhead without improving outcomes or reducing risk. UC provisioning automation helps organizations reallocate these valuable resources to more strategic initiatives.
READ MORE: How User Provisioning Software Enhances UC User Experience
Delayed Access and Productivity Loss
New employees often wait days or weeks for complete UC access, limiting their ability to contribute effectively from day one. Meanwhile, departing employees may retain access longer than necessary, creating ongoing security risks that manual processes struggle to address consistently.
These challenges demonstrate why manual user provisioning process flows are outdated. Automated UC provisioning solutions address each limitation while creating new capabilities that manual processes simply cannot deliver.
Step-by-Step: How Automation Tools Transform Your User Provisioning Process Flow
Step 1: Automated User Request Initiation
Tool: Self-Service Provisioning Portal
Instead of IT fielding phone calls and emails, employees and managers access a centralized self-service portal that presents role-based request options. The portal displays available UC services, required approvals, and estimated completion times.
Key Features:
- Role-based service catalogs that show only relevant UC options
- Guided request forms that capture all necessary information
- Real-time status tracking for pending requests
- Mobile-responsive design for hybrid work environments
Workflow Impact: Reduces initial request processing time from hours to minutes while ensuring complete information capture.
Step 2: Intelligent Routing and Approval
Tool: Workflow Engine with Automated Approval Chains
The system automatically routes requests through appropriate approval chains based on role, department, and requested access levels. Managers receive notifications with all relevant context and can approve requests with a single click.
Key Features:
- Dynamic approval routing based on organizational hierarchy
- Risk-based approval requirements (high-risk requests require additional approvals)
- Mobile notifications for managers
- Automated escalation for delayed approvals
Workflow Impact: Eliminates approval bottlenecks while maintaining appropriate oversight and compliance controls.
Step 3: Template-Based Account Creation
Tool: RBAC (Role-Based Access Control) Template Engine
Once approved, the system uses pre-configured RBAC templates to create consistent user profiles across all UC platforms. Templates ensure every user receives identical security settings and access permissions based on their role.
Key Features:
- Pre-built templates for common roles (executive, manager, employee, contractor)
- Custom template creation for unique organizational needs
- Inheritance hierarchies that simplify permission management
- Security baseline enforcement across all platforms
Workflow Impact: Reduces configuration errors by over 90% while ensuring consistent security implementation.
READ MORE: The 5 Must-Have Automation Features in a UC Provisioning Tool
Step 4: Integrated Multi-Platform Deployment
Tool: Universal Connector Framework
The system simultaneously provisions accounts across all integrated UC platforms—voice systems, video conferencing, messaging, and collaboration tools. Each platform receives properly formatted configurations without manual intervention.
Key Features:
- Native connectors for major UC platforms (Teams, Webex, Zoom, etc.)
- Real-time provisioning status across all systems
- Automatic retry logic for failed deployments
- Configuration validation before deployment
Workflow Impact: Complete UC profile creation in minutes rather than days, with guaranteed consistency across platforms.
Step 5: Automated Validation and Testing
Tool: Provisioning Validation Suite
The system automatically tests new accounts to ensure proper configuration and connectivity. Users receive welcome emails with login credentials and quick-start guides, while IT gets confirmation that all services are functioning correctly.
Key Features:
- Automated login testing for all provisioned services
- Connectivity verification across UC platforms
- Automated welcome email delivery with personalized quick-start guides
- Exception reporting for failed validations
Workflow Impact: Ensures new employees have working UC access from day one while reducing support tickets.
Step 6: Comprehensive Audit Trail Generation
Tool: Compliance and Audit Dashboard
Every action in the user provisioning and deprovisioning process is automatically logged with timestamps, approvers, and specific changes made. The system generates comprehensive audit trails that support compliance requirements and security investigations.
Key Features:
- Real-time audit log generation with detailed change tracking
- Pre-built compliance reports for common regulations
- Advanced filtering and search capabilities
- Automated retention policies for audit data
Workflow Impact: Eliminates manual documentation while providing bulletproof compliance evidence.
Step 7: Automated Deprovisioning and Access Termination
Tool: Lifecycle Management Engine
When employees leave, the system instantly revokes access across all UC platforms simultaneously. HR system integration triggers immediate account deactivation, while the audit trail documents exactly when and how access was terminated.
Key Features:
- Instant access termination across all integrated platforms
- HR system integration for automatic trigger events
- Grace period configuration for temporary access needs
- Asset recovery tracking for company devices and licenses
Workflow Impact: Immediate security risk elimination while maintaining detailed compliance records.
READ MORE: How User Provisioning Software Enhances UC User Experience
The Strategic Impact of Your Automated User Provisioning Process Flow
Organizations that embrace automated UC user provisioning processes gain advantages that extend far beyond administrative efficiency. These systems create strategic capabilities that support business growth while strengthening security posture.
- Enhanced Security Posture: Consistent security implementation and immediate access termination reduce breach risks while ensuring compliance with evolving regulatory frameworks.
- Improved Employee Experience: Faster onboarding and reliable access eliminate frustrations that impact productivity and satisfaction, particularly for remote and hybrid workers.
- IT Resource Optimization: Automating routine tasks frees IT teams to focus on innovation and strategic initiatives that drive competitive advantage.
- Operational Resilience: Documented processes and comprehensive audit trails support business continuity while providing evidence for compliance and security investigations.
- Future Readiness: Automated systems adapt quickly to new UC technologies and changing business requirements, ensuring organizations can capitalize on emerging opportunities.
READ MORE: How Automated UC User Provisioning Meets Regulatory Needs
Conclusion
As UC environments grow more complex and security requirements become stricter, manual user provisioning process flows create operational risks that organizations can no longer afford. The choice is clear: continue struggling with error-prone, resource-intensive account provisioning processes, or embrace automated UC provisioning that delivers speed, security, and scalability.
The step-by-step approach outlined above demonstrates how automation tools transform every phase of the user access provisioning process—from initial request through final deprovisioning. Organizations that implement these workflows position themselves for sustainable growth, while those that delay face mounting challenges that can compound over time.
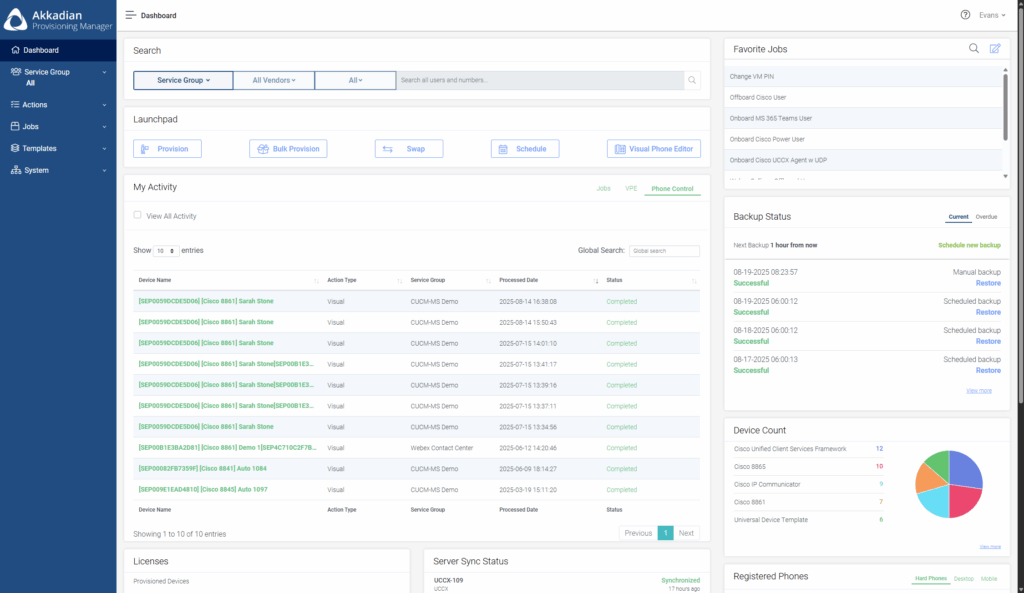
Ready to streamline your user provisioning and deprovisioning process? Akkadian Provisioning Manager delivers the automation tools showcased in this guide to secure, accelerate, and scale your UC environment without compromising control or compliance. Schedule a demo to see how these specific tools eliminate provisioning bottlenecks while strengthening your security posture.